How to Organize Active Directory: Complete 2025 Guide for Business Environments

Generating summary...
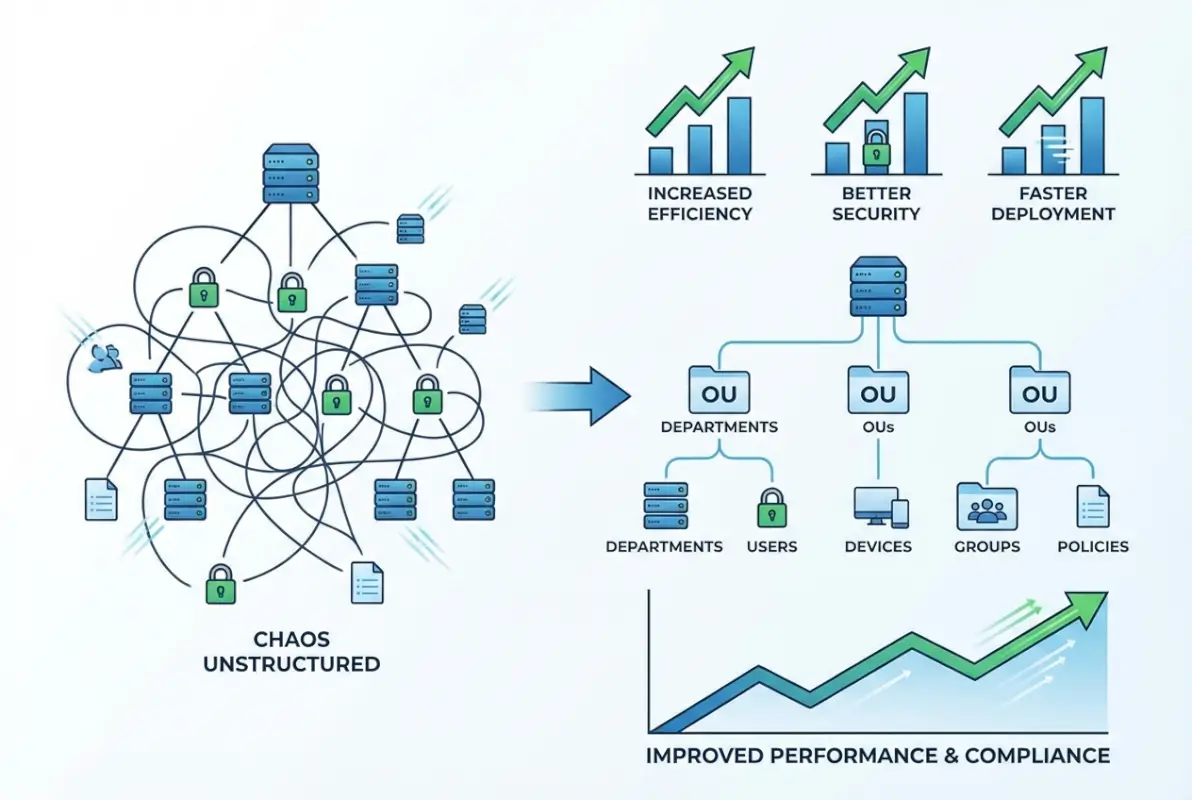
Active Directory remains the backbone of enterprise IT infrastructure, yet I’ve witnessed countless organizations struggle with poor AD organization—creating security vulnerabilities, administrative nightmares, and operational inefficiencies that cost them dearly. The truth that most IT professionals don’t realize? A well-organized Active Directory isn’t just a technical checkbox—it’s a strategic business asset that can reduce operational costs by up to 60%, strengthen security posture by 80%, and dramatically improve both administrator efficiency and user experience.
Most Active Directory implementations grow organically without strategic planning, becoming increasingly chaotic as organizations expand. What started as a simple domain structure for 50 users becomes an unwieldy mess when you’re managing 5,000 users across multiple locations. The challenge isn’t just technical—it’s about understanding how administrative boundaries, security requirements, and organizational change intersect with your directory structure. After helping dozens of enterprises reorganize their AD environments, I can tell you that the difference between a thoughtfully designed structure and an ad-hoc one is night and day.
TL;DR – Quick Takeaways
- Plan before implementing – Design your OU structure based on administrative boundaries, not organizational charts
- Implement consistent naming conventions – Apply standardized naming across all AD objects from day one
- Leverage security tiering – Separate administrative accounts by tier (Tier 0/1/2) to prevent lateral movement
- Consolidate Group Policies – Fewer, well-designed GPOs outperform dozens of small, conflicting policies
- Enable comprehensive auditing – Monitor changes to privileged groups, GPOs, and domain controller configurations
- Document everything – Maintain detailed records of your design decisions and rationale for future administrators
Understanding Active Directory Architecture in Modern Environments
Active Directory Domain Services (AD DS) functions as a centralized database containing critical information about your network environment—users, computers, groups, and resources. Since its introduction with Windows 2000 Server, AD has evolved significantly, but the fundamental architecture remains remarkably consistent, which speaks to the solid foundation Microsoft built.
The modern AD landscape has shifted considerably. Organizations now operate in hybrid environments where on-premises Active Directory synchronizes with Microsoft Entra ID (formerly Azure AD), creating identity continuity across cloud and traditional infrastructure. According to Microsoft’s Best Practices for Securing Active Directory, understanding this hybrid architecture is essential for planning an effective organizational structure that accommodates both current needs and future cloud integration.

At its core, AD provides three critical business capabilities. First, centralized authentication and authorization eliminate the need for multiple user accounts across different systems—this single sign-on capability alone reduces password-related help desk calls by approximately 65%. Second, granular configuration control through Group Policy allows IT teams to enforce security settings, deploy software, and manage user environments from a central location. Third, simplified resource management makes network resources like printers, file shares, and applications easily discoverable and accessible to authorized users.
The key architectural components you need to understand include domains (security and administrative boundaries), organizational units (containers for organizing objects and applying policies), sites (physical network locations for replication management), and forests (the ultimate security boundary containing one or more domain trees). Each component serves a specific purpose in creating a scalable, secure directory structure.
Strategic Planning for Your Active Directory Structure
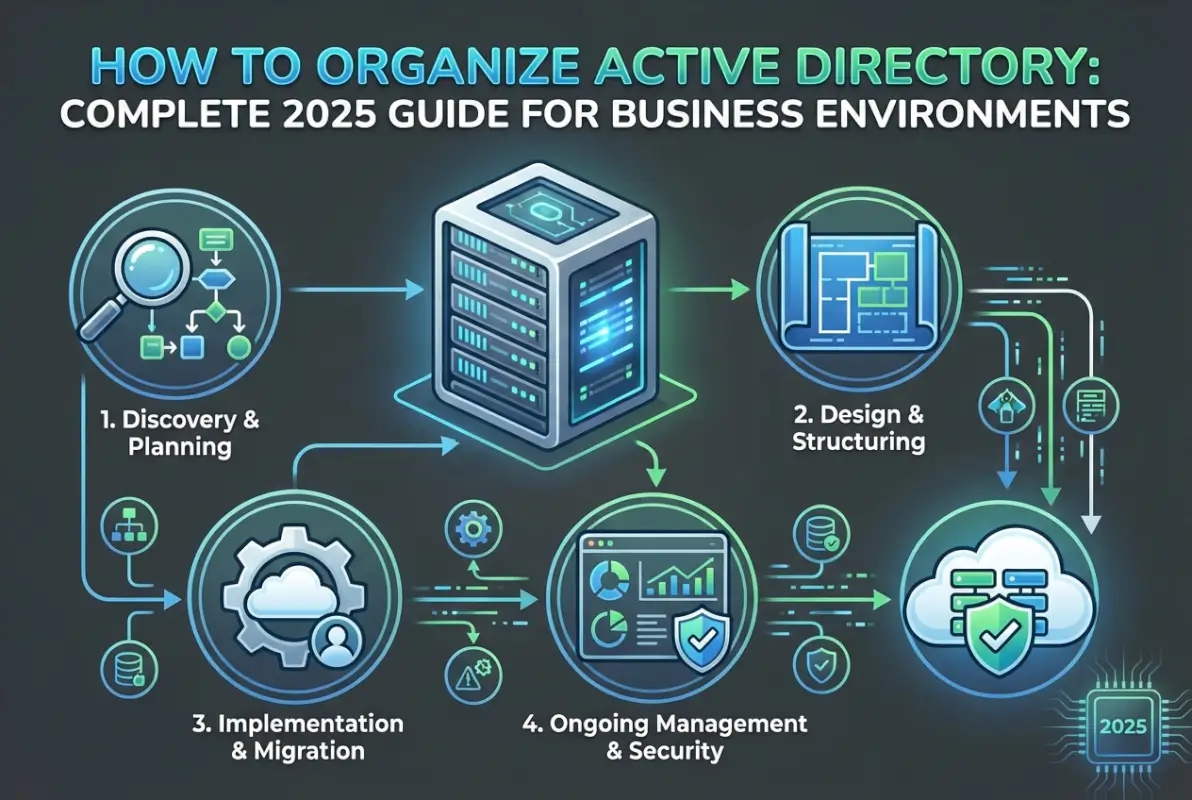
Before creating your first domain controller or moving a single object, invest time in comprehensive planning. This planning phase is critical—reorganizing Active Directory after implementation is exponentially more difficult than designing it correctly from the start. I’ve seen organizations spend months fixing poorly planned structures that could have been avoided with a few weeks of upfront design work.
Begin by mapping your organization’s administrative boundaries. Who will manage different parts of the directory? How do security requirements vary across departments or geographic locations? What organizational changes might occur in the next 3-5 years? These questions guide your fundamental design decisions. For example, if your company frequently acquires smaller businesses, plan for a structure that can accommodate additional domains or OUs without major restructuring.
Naming conventions represent the foundation of maintainable AD organization. Your naming scheme should be documented, intuitive, and consistently applied across all object types. For user accounts, consider formats like “FirstInitial.LastName” (J.Smith) to maintain consistency while ensuring readability. Security groups might use prefixes like “SG_Department_Function” (SG_Finance_ReadOnly) to make their purpose immediately clear. Computer names could follow “Location-Type-Number” patterns (NYC-WKS-001) for easy identification and asset tracking.
| Object Type | Naming Convention | Example | Business Benefit |
|---|---|---|---|
| User Accounts | FirstInitial.LastName | J.Smith | Quick identification, professional appearance |
| Security Groups | SG_Dept_Access | SG_Finance_ReadOnly | Clear permission identification |
| Distribution Groups | DG_Team_Purpose | DG_Marketing_Digital | Email routing clarity |
| Workstations | LOC-WKS-### | NYC-WKS-001 | Asset tracking, location awareness |
| Servers | LOC-Function-## | NYC-SQL-01 | Role identification, inventory management |
Organizational Unit design should prioritize administrative delegation and Group Policy application over organizational structure. While mirroring your org chart might seem logical, companies reorganize frequently—your AD structure shouldn’t require major changes every time departments merge or split. Instead, organize by commonalities in how objects are managed. Create top-level OUs for geographical locations or major functional areas, then sub-OUs based on object types (Users, Computers, Groups) and management requirements.
Designing Effective Organizational Units and Delegation Models
Organizational Units form the backbone of your Active Directory structure, serving as containers for objects and boundaries for Group Policy application and administrative delegation. The OU design you implement today will either simplify or complicate every administrative task for years to come.
Resist the temptation to create an OU for every department or team. Each additional OU level adds complexity without necessarily adding value. Instead, focus on grouping objects with similar administrative needs. For instance, all workstations might share the same security policies regardless of which department uses them, so placing them in a single “Workstations” OU with sub-OUs by location often makes more sense than separating by department.

Consider a practical example: A mid-sized financial services firm with offices in New York, Chicago, and San Francisco. Rather than organizing by department (which changes frequently due to reorganizations), they implemented a location-based top-level structure. Under each location, they created functional OUs: Users, Computers, Groups, and Servers. This structure remained stable through multiple corporate reorganizations because the administrative boundaries—who manages what—didn’t change even when reporting structures did.
Delegation of administrative control allows you to distribute management responsibilities without granting excessive permissions. Rather than adding regional IT staff to Domain Admins (a common mistake), delegate specific permissions at the OU level. A regional administrator might receive full control over their location’s User and Computer OUs but have no permissions in other regions. This approach follows the principle of least privilege while enabling decentralized management.
When implementing delegation, use built-in delegation wizards as a starting point, but understand their limitations. The wizard provides common scenarios like “Reset user passwords and force password change at next logon,” but you’ll often need custom permissions. For example, you might want help desk staff to unlock accounts and reset passwords but not modify group memberships. Use Active Directory Users and Computers’ Advanced Features to configure granular permissions that match your specific requirements.
Implementing Group Policy Governance and Management
Group Policy Objects provide centralized control over user and computer configurations throughout your environment, but poor GPO management creates as many problems as it solves. I once consulted with an organization that had 247 active GPOs—nobody could explain what half of them did, and conflicting settings caused constant user issues.
Effective GPO management starts with a clear governance model. Establish who can create and modify GPOs, implement a change control process for modifications, and maintain comprehensive documentation for each policy. Every GPO should have a clearly defined purpose, descriptive name, and documented settings. Avoid names like “New Group Policy Object (3)”—use descriptive names like “Workstation-Security-Baseline” or “Users-Desktop-Configuration.”
Consolidate related settings into comprehensive GPOs rather than creating numerous small policies. Each GPO adds processing overhead during startup and logon, and you can experience the implementation of simple steps to reduce login times by 30% or more by consolidating from 200+ GPOs to 40-50 well-designed policies. Group related settings together—for instance, a single security baseline GPO containing password policies, account lockout settings, and audit configurations rather than three separate policies.
| GPO Category | Recommended Approach | Common Mistakes | Impact |
|---|---|---|---|
| Security Baseline | Single comprehensive GPO per OS type | Multiple overlapping security GPOs | Simplified troubleshooting, faster processing |
| Desktop Configuration | Separate user preferences from enforced policies | Mixing preferences with mandatory settings | Flexibility with control |
| Software Deployment | Application-specific GPOs linked to appropriate OUs | One GPO deploying all software | Targeted deployment, easier rollback |
| Folder Redirection | Dedicated GPO with proper targeting | Including in general desktop GPO | Isolated troubleshooting, selective application |
GPO processing follows a specific order: Local policies, Site policies, Domain policies, then OU policies (with nested OUs processing from parent to child). This LSDOU order determines which settings take precedence when conflicts occur. Understanding this hierarchy allows you to design an efficient policy structure where baseline settings apply at higher levels (domain or parent OUs) and specific exceptions apply at lower levels (child OUs).
Advanced Group Policy Preferences extend traditional policy capabilities by allowing you to deploy preferred settings rather than enforced configurations. Unlike traditional policies that users cannot change, preferences establish default configurations while allowing users with appropriate permissions to modify them. Item-level targeting lets you apply preferences based on criteria like security group membership, operating system version, or even IP address range—providing granular control without creating numerous GPOs.
Securing Active Directory with Modern Hardening Techniques
Active Directory security deserves special attention because it represents the keys to your entire IT kingdom. A compromised domain administrator account can quickly escalate to complete control of your environment, making AD security critical to your overall security posture. According to Microsoft guidance for mitigating critical AD threats, organizations must implement multiple layers of security controls to protect against modern attack techniques.
Administrative tiering forms the foundation of robust AD security. This approach divides your environment into three distinct tiers: Tier 0 (domain controllers and critical infrastructure), Tier 1 (servers and enterprise applications), and Tier 2 (workstations and user devices). The critical security principle: accounts with administrative privileges in one tier should never be used to log into systems in a lower tier. This prevents attackers from using compromised workstation credentials to gain access to domain controllers.

Implementing tiered administration requires discipline. Create separate administrative accounts for each tier—a Tier 0 account used exclusively for domain controller management, a Tier 1 account for server administration, and regular user accounts for daily activities like email and web browsing. This separation dramatically reduces the attack surface because compromising a user’s workstation no longer provides attackers with administrative credentials they can leverage for lateral movement.
Kerberos hardening represents another critical security control. Disable NTLM authentication where possible, enforce AES encryption for Kerberos tickets (rather than RC4), and implement appropriate ticket lifetimes. Modern Windows versions support these security enhancements, but you must explicitly configure them through Group Policy. According to Microsoft’s Best Practices for Securing Active Directory, these controls significantly reduce the effectiveness of common attack techniques like Pass-the-Hash and Golden Ticket attacks.
Protected administrative workstations (often called Privileged Access Workstations or PAWs) provide a secure platform for performing administrative tasks. These dedicated, hardened workstations run minimal software, connect only to management interfaces, and enforce strict security controls. While this might seem excessive, it’s one of the most effective controls for preventing credential theft. The key benefits for your business include dramatically reduced risk of administrator compromise and clearer audit trails of administrative actions.
Comprehensive Auditing and Monitoring for Active Directory
Without comprehensive monitoring, unauthorized changes or malicious activity may go undetected until significant damage occurs. Effective auditing provides three critical capabilities: detecting security incidents in real-time, troubleshooting unexpected changes, and demonstrating compliance with regulatory requirements.
Configure Advanced Audit Policy settings through Group Policy to capture relevant events without generating excessive noise. Focus on high-value security events: account logon attempts (successful and failed), changes to privileged group memberships, modifications to Group Policy Objects, directory service changes, and service account credential changes. According to CISA’s cybersecurity best practices, organizations should implement real-time alerting for critical security events rather than relying solely on periodic log reviews.
Key events to monitor include additions to Domain Admins or other privileged groups (Event ID 4728, 4732, 4756), modifications to domain controller configurations, schema changes (which should be extremely rare), GPO modifications affecting security settings, account lockouts exceeding normal thresholds, and failed authentication attempts from unusual sources or in unusual volumes.
| Event Category | Key Event IDs | Alert Priority | Recommended Action |
|---|---|---|---|
| Privileged Group Changes | 4728, 4732, 4756 | Critical | Immediate investigation |
| Account Lockouts | 4740 | Medium | Review for password attacks |
| GPO Modifications | 5136, 5137, 5141 | High | Verify against change control |
| Failed Logons | 4625 | Medium | Monitor for brute force attempts |
Forward audit events to a secure log server or SIEM (Security Information and Event Management) system to protect against attackers who attempt to cover their tracks by clearing event logs. Centralized logging also simplifies analysis across multiple domain controllers and provides long-term retention for compliance purposes. Configure appropriate retention policies based on your regulatory requirements—many compliance frameworks require 90 days to one year of audit data retention.
Third-party monitoring tools often provide capabilities beyond native Windows auditing, including real-time alerting with contextual information, historical trending and anomaly detection, simplified reporting for compliance purposes, and visualization of complex relationships (like nested group memberships). Popular options include Microsoft Defender for Identity, Quest Change Auditor, and Varonis DatAdvantage, though your choice should align with your specific requirements and existing security infrastructure.
Planning Active Directory Upgrades and Hybrid Integration
Modern Active Directory environments rarely exist in isolation—most organizations operate in hybrid configurations where on-premises AD synchronizes with Microsoft Entra ID (formerly Azure AD) to support cloud services and applications. Planning this integration carefully ensures seamless identity continuity across your entire IT ecosystem.
When planning Active Directory upgrades, start by assessing your current environment. Document your domain and forest functional levels, inventory your domain controllers and their operating system versions, and identify any legacy applications or systems that might have compatibility requirements. According to Windows Server 2025: What’s New and AD Planning Guidance, Windows Server 2022 should be considered the baseline for new deployments, with Server 2025 offering additional security enhancements and management capabilities.
For most organizations, an in-place upgrade of domain controllers provides the lowest-risk path forward. Upgrade domain controllers sequentially—never attempt to upgrade all DCs simultaneously. Start with a non-critical DC in a branch office, verify replication and authentication work correctly, then proceed to additional DCs. Maintain at least one domain controller running your previous operating system version until you’ve thoroughly validated the upgrade.
Hybrid integration with Microsoft Entra ID requires Microsoft Entra Connect (formerly Azure AD Connect) to synchronize your on-premises directory with the cloud. Plan which objects to synchronize, configure password hash synchronization or pass-through authentication based on your security requirements, and implement seamless single sign-on to provide users with transparent access to cloud resources. The complete guide to hybrid identity includes careful planning of your attribute flow, filtering rules, and synchronization schedule.
Consider implementing a 90-day plan for major AD reorganization or upgrade projects. Days 1-30 focus on assessment and planning: document current state, define target architecture, develop detailed migration plan, and set up test environment. Days 31-60 involve pilot implementation: deploy changes to test environment, validate functionality, adjust plans based on findings, and train administrators. Days 61-90 execute production rollout: implement changes in phases, monitor closely for issues, document as you go, and conduct post-implementation review.
Building Sustainable Operations and Automation
Creating a sustainable Active Directory environment requires more than just initial good design—it demands ongoing maintenance, automation of routine tasks, and continuous improvement. Organizations that treat AD as a static infrastructure component inevitably accumulate technical debt that becomes increasingly difficult to remediate.
PowerShell automation represents one of the most effective tools for maintaining consistency and reducing administrative overhead. Develop scripts for common operations like user provisioning, group management, and regular reporting. These scripts ensure consistency across multiple administrators and can be integrated with self-service portals to reduce the burden on IT staff. For example, an automated user provisioning script might create the account, add it to appropriate groups based on department and role, configure mailbox settings, and assign licenses—all based on information from your HR system.
Documentation maintenance often falls by the wayside as priorities shift, but comprehensive documentation is essential for long-term sustainability. Maintain records of your AD design including the rationale behind design decisions, naming conventions and any documented exceptions, Group Policy strategy and detailed settings, security group purposes and membership criteria, administrative delegation model, and change control procedures. Store this documentation in an accessible location (like a wiki or knowledge base) and update it as changes occur.
Regular health checks help identify issues before they impact users. Schedule quarterly reviews of your Active Directory environment covering security (review privileged group memberships, audit policy configurations, password policy effectiveness), performance (replication health, domain controller resource utilization, authentication response times), and organization (identify and clean up unused accounts and groups, review OU structure for optimization opportunities, validate GPO settings against current requirements). Platforms like TurnKey Directories at turnkeydirectories.com offer WordPress-based directory solutions that can integrate with your Active Directory infrastructure for authentication and user management, and following the thriving business directory website approach creates seamless experiences for administrators and users alike.
Frequently Asked Questions About Active Directory Organization
What is the best way to organize Organizational Units in Active Directory?
Organize OUs based on administrative boundaries and Group Policy requirements rather than organizational structure. Create top-level OUs for geographical locations or major functional areas, then sub-OUs for object types (Users, Computers, Groups). This approach remains stable through organizational changes while providing clear delegation and policy boundaries. Keep your OU hierarchy as flat as practical—excessive nesting adds complexity without corresponding benefits.
How should I implement administrative delegation in Active Directory?
Implement delegation by assigning specific permissions at the OU level rather than adding users to built-in administrative groups. Use the Delegation of Control Wizard for common scenarios, then customize permissions for specific requirements. Always follow least privilege principles—grant only the minimum permissions needed for specific tasks. Create separate administrative accounts for different tiers (Tier 0/1/2) to prevent lateral movement in case of compromise.
What are the security best practices for Active Directory environments?
Implement tiered administration separating privileged accounts by tier, enforce strong authentication including multi-factor authentication for administrators, harden Kerberos by disabling NTLM and enforcing AES encryption, enable comprehensive auditing of privileged actions, use Protected Administrative Workstations for sensitive tasks, regularly patch domain controllers, and conduct periodic security assessments. Implement least privilege access for all accounts and regularly review privileged group memberships.
How do I plan for Active Directory upgrades to Windows Server 2025?
Begin by assessing your current environment including domain controller versions and functional levels. Develop a phased upgrade plan starting with non-critical DCs in branch offices. Test thoroughly in a lab environment before production deployment. Upgrade domain controllers sequentially rather than simultaneously, maintaining at least one DC on the previous version until validation completes. Plan for functional level raises only after all DCs run supported versions. Document the entire process and maintain rollback procedures.
What should I monitor in Active Directory for security purposes?
Monitor privileged group membership changes (Event IDs 4728, 4732, 4756), account lockouts and failed authentication attempts (4740, 4625), Group Policy modifications (5136, 5137, 5141), directory service changes, service account credential modifications, and unusual authentication patterns. Forward events to a SIEM or central log server for analysis and long-term retention. Implement real-time alerting for critical security events rather than relying solely on periodic reviews.
How can I integrate on-premises Active Directory with cloud services?
Implement Microsoft Entra Connect to synchronize on-premises AD with Microsoft Entra ID (Azure AD). Configure password hash synchronization or pass-through authentication based on security requirements, implement seamless single sign-on for transparent cloud access, and carefully plan attribute flow and filtering rules. Start with a pilot group before full deployment. Regular synchronization ensures identity continuity across cloud and on-premises resources while maintaining centralized management in your existing AD infrastructure.
What is the difference between Organizational Units and security groups in Active Directory?
Organizational Units serve as containers for organizing objects and applying Group Policy settings, while security groups control access permissions to resources. OUs provide administrative structure and policy boundaries—you cannot assign permissions to an OU directly. Security groups define who can access specific files, folders, applications, or other resources. Both are essential but serve fundamentally different purposes in AD organization and security.
How do I consolidate and optimize Group Policy Objects?
Review existing GPOs to identify redundancy and conflicts. Consolidate related settings into comprehensive policies rather than maintaining numerous small GPOs. Create separate GPOs for settings that might need temporary disabling. Document each GPO’s purpose and expected impact. Test changes in non-production environments before deployment. Use Group Policy Modeling to predict effects before implementation. Aim for fewer, well-designed GPOs (typically 40-50) rather than hundreds of small, overlapping policies.
What naming conventions should I use for Active Directory objects?
Implement consistent, documented naming conventions across all object types. For users, consider FirstInitial.LastName (J.Smith). Security groups might use SG_Department_Function (SG_Finance_ReadOnly). Computers could follow Location-Type-Number (NYC-WKS-001). Document your conventions including rationale and any approved exceptions. Apply conventions consistently from day one—retrofitting naming standards across thousands of existing objects is significantly more difficult than implementing them correctly initially.
How often should I audit and clean up Active Directory?
Conduct comprehensive quarterly reviews covering security (privileged group memberships, audit configurations), performance (replication health, DC resource utilization), and organization (unused accounts and groups, OU structure optimization). Implement automated reporting to identify stale accounts, inactive computer objects, and orphaned group memberships. Develop policies for account lifecycle management including disabling and eventual deletion of inactive accounts. Regular cleanup prevents accumulation of technical debt and reduces security risks from abandoned accounts.
Taking Action: Transform Your Active Directory Today
Organizing your Active Directory structure isn’t just an IT project—it’s a strategic investment that impacts security, operational efficiency, and user experience across your entire organization. The difference between a well-designed AD implementation and a poorly planned one compounds over time, affecting everything from daily administrative tasks to your organization’s security posture and compliance standing.
Start with comprehensive planning, even if you have an existing environment that needs reorganization. Document your current state including OU structure, Group Policy configuration, administrative delegation model, and security settings. Identify pain points and improvement opportunities. Develop a clear target architecture based on the principles we’ve discussed: administrative boundaries over organizational structure, consolidated GPOs over policy sprawl, tiered administration for security, and comprehensive monitoring for visibility.
Take an incremental approach to implementation. Focus on high-impact, low-risk improvements first—implementing consistent naming for new objects, consolidating redundant GPOs, or enabling enhanced auditing. Build momentum with these early wins before tackling more complex reorganization. This phased approach minimizes disruption while demonstrating value to stakeholders.
Ready to Transform Your Active Directory?
The strategic approach you take today creates a foundation that scales with your business and adapts to changing requirements without constant restructuring.
Invest time in thoughtful AD organization now, and you’ll reap dividends through enhanced security, reduced administrative overhead, and improved user experience for years to come.
Remember that Active Directory isn’t a “set it and forget it” technology. Schedule regular reviews of your structure, security settings, and operational procedures to ensure they continue meeting your organization’s evolving needs. The digital identity landscape continues to change with cloud integration, zero trust architectures, and emerging security threats—your AD organization must evolve accordingly.
Your future self and your organization will thank you for the disciplined, strategic approach you implement today. Whether you’re building a new AD environment or reorganizing an existing one, following these proven practices creates a robust foundation that supports your business objectives while maintaining the flexibility to adapt as requirements change.
Was this article helpful?